We covered Brim which is an open source packet and log analyzer. Brim has powerful features that make it ideal for large packet capture files because it has GUI interface combined with powerful search engine and query system. We also covered two practical scenarios where we used Brim to investigate malware infection and crypto mining activity. This was part of TryHackMe Brim SOC Level 1 pathway.
What is Brim in Digital Forensics
Brim is presented as a versatile tool essential for cybersecurity professionals, especially in the domains of packet and log analysis. It is compared with other notable tools such as Zeek, Wireshark, and NetworkMiner, each having distinct strengths. Brim is especially valued for its ability to manage large-sized pcap files and for providing a GUI interface for better visualization and accessibility.
Brim’s dual strengths lie in its search engine capabilities and its GUI-based data visualization. It not only makes packet analysis user-friendly but also supports custom and default queries. Users can navigate large datasets with ease, extract meaningful insights, and render them in visual formats, enhancing the interpretability of network traffic.
Comparison with Other Coputer Forensics Tools
Wireshark, suitable for medium-sized files, lacks the efficiency of Brim in handling larger datasets. Zeek, though powerful for log analysis and capable of generating 50+ types of logs, lacks a GUI. Brim, thus, bridges this gap by offering intuitive interfaces and extensive capabilities for both log and packet analysis.
Brim supports both default queries (predefined and GUI-integrated) and custom queries (user-defined with syntax). Logical operators like and, or, not, filtering using ==, and statistical functions like count and sort allow analysts to craft powerful expressions. Utilities such as cut and unique enable extraction of clean, refined datasets from raw logs.
Brim Interface Overview
The interface includes panes for selecting pcaps (“pools”), executing queries (default/custom), and reviewing results. Each packet detail can be drilled down to view associated log types like DNS, connection, or HTTP. Visualization components support dynamic filtering and exporting of findings for external analysis in tools like Zeek or Wireshark.
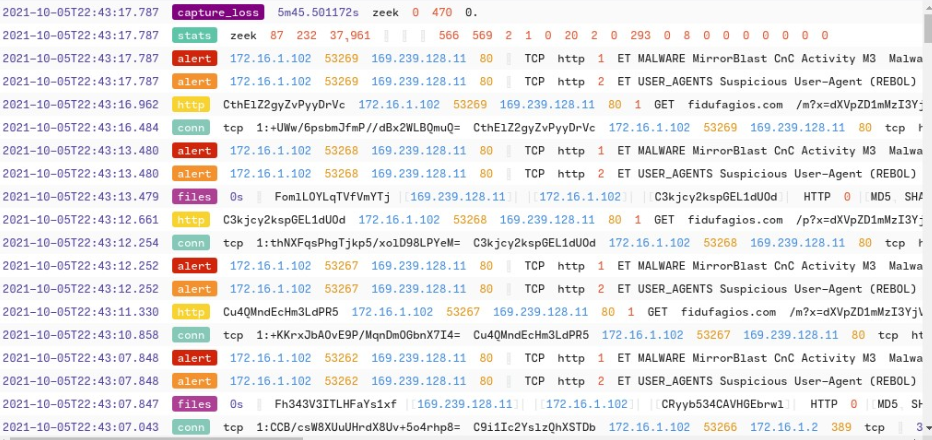
Brim integrates Suricata IDS/IPS, enhancing detection through alerts categorized by source, subnet, and threat type. These alerts assist in corroborating suspicious behavior previously detected via custom queries. Specific alerts for trojans and unknown traffic affirm the earlier conclusions.
Key IOCs include IP addresses, domains, file names, and hashes linked to the malware. By methodically analyzing logs, the analyst maps these indicators and validates them against known threat intel databases, ensuring robust incident detection and response.
Video Highlights
TryHackMe Brim Room Answers
Look at the details of the first NTP log that appear on the dashboard. What is the “duration” value?
Look at the details of the STATS packet log that is visible on the dashboard. What is the “reassem_tcp_size”?
Investigate the conn logfile. What is the number of the identified city names?
Investigate the Suricata alerts. What is the Signature id of the alert category “Potential Corporate Privacy Violation”?
What is the number of CobaltStrike connections using port 443?
There is an additional C2 channel in used the given case. What is the name of the secondary C2 channel?
How many connections used port 19999?
What is the name of the service used by port 6666?
What is the amount of transferred total bytes to “101.201.172.235:8888”?
What is the detected MITRE tactic id?




